Automated, insightful, all-in-one protection
Automated
Trend Micro Apex One™ protection offers advanced automated threat detection and response against an ever-growing variety of threats, including fileless and ransomware. Our cross-generational blend of modern techniques provides highly tuned endpoint protection that maximizes performance and effectiveness.
Insightful
Get actionable insights, expanded investigative capabilities, and centralized visibility by using an advanced EDR toolset, strong SIEM integration, and an open API set. You have the option to perform correlated, extended threat investigations that go beyond the endpoint and augment your security teams with a managed detection and response service.
All-in-one
In an evolving technological landscape, you need security that goes beyond traditional antivirus. Apex One offers threat detection, response, and investigation within a single agent. Eliminate multiple vendors and consoles and gain deployment flexibility through both SaaS and on-premises deployment options.
Download Datasheet – Endpoint Security with Apex One
Apex One System Requirements
Minimum recommended agent requirements
Agent Operating Systems
- Windows 7 (6.1)
- Windows 8.1 (6.2/6.3)
- Windows 10 (10.0)
- Windows Server 2008 R2 (6.1)
- Windows Server 2012 (6.2)
- Windows Server 2012 R2 (6.3)
- Windows Server 2016 (10)
- Windows Server 2019
- macOS® High Sierra 10.13
- macOS Sierra 10.12
- OS X® El Capitan 10.11
- OS X Yosemite 10.10 or later
- OS X Mavericks 10.9 or later
- OS X Mountain Lion 10.8.3 or later
- OS X Lion 10.7.5 or later (64-bit only)
Agent Platform
Processor: 300 MHz Intel Pentium or equivalent (Windows 7, 8.1, 10 family) and Intel® Core™ processor for Mac
- 1.0 GHz minimum (2.0 GHz recommended) Intel Pentium or equivalent (Windows Embedded POSReady7)
- 1.4 GHz minimum (2.0 GHz recommended) Intel Pentium or equivalent (Windows 2008 R2, Windows 2016 family, Windows 2019 family)
Memory:
- 512 MB minimum (2.0 GB recommended) with at least 100 MB exclusively for Apex One (Windows 2008 R2, 2012 family)
- 1.0 GB minimum (2.0 GB recommended) with at least 100 MB exclusively for Apex One (Windows 7 (x86), 8.1 (x86), Windows Embedded POSReady 7, 10 (x64) family)
- 2.0 GB minimum (4.0 GB recommended) with at least 100 MB exclusively for Apex One (Windows 7 (x64), 8.1 (x64), 10 (x64) family)
- 512 MB minimum for Apex One on Mac
Disk Space: 1.5GB minimum (3GB recommended for all products) for Windows, 300 MB minimum for Mac
Advanced detection techniques
Apex One leverages a blend of cross-generational threat techniques to provide the broadest protection against all types of threats, giving you:

Pre-execution and runtime machine learning

More accurate detection of advanced malware, such as fileless, living off the land, and ransomware threats

Noise-cancelling techniques – like census and safelisting – throughout every layer of detection to dramatically reduce false positives

Effective protection against scripts, injection, ransomware, memory, and browser attacks through innovative behavior analysis
Ultimate protection against vulnerabilities
More than just a scan, Apex One Vulnerability Protection uses a host-based intrusion prevention system (HIPS) to virtually patch known and unknown vulnerabilities before a patch is available or deployable:

Eliminating risk exposure by shielding vulnerabilities through innovative virtual patching capabilities and world-class research

Extending protection to critical platforms and physical or virtual devices

Reducing recovery and emergency patching downtime

Identifying vulnerabilities based on CVE, MS-ID, and severity

Detecting more vulnerabilities than any other vendor by leveraging our industry-leading vulnerability research
Integrated detection and response
Leverage advanced detection techniques that allow you to discover and respond to threats before they compromise data. With Trend Micro Vision One™, you gain full-featured XDR capabilities to deepen detection and response capabilities and extend them across multiple security layers for broad visibility and response to threats impacting the entire organization.
Experience XDR with Trend Micro Vision One with automatic free access for 10% of licensed users*. Secure those most at risk, and improve detection and response for your organization.
*Free XDR licenses do not include integrated response actions

Hunt for indicators of attack (IoA) and define the attacker’s intent in real time

Sweep user timelines (telemetry) for indicators of compromise (IoCs) to determine the impact of targeted attacks
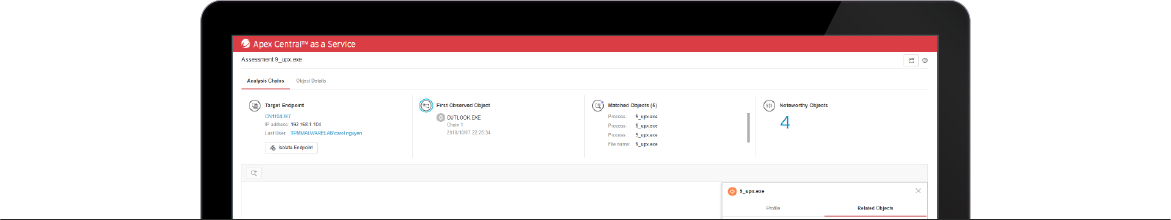
Employ an interactive root cause analysis diagram to drill down on a detection, and respond by isolating or terminating processes and updating protection points
Have the option to go beyond a single vector approach by correlating events across email, endpoints, servers, cloud workloads, and networks
Effective security for your sensitive data Protect your sensitive data, on or off network, for maximum visibility and control. Endpoint encryption,* integrated DLP, and device control:
- Cover the broadest range of devices, applications, and file types
- Assist with most regulatory compliance, including GDPR
- Protect data with full-disk, folder, file, and removable media encryption
- Set granular policies for device control and data management
- Manage Microsoft® BitLocker®, and Apple® FileVault® encryption keys
*Endpoint encryption is available as a separate agent.
Enhanced application control against malicious software Prevent unknown and unwanted applications from executing on your corporate endpoints. Trend Micro Apex One™ Application Control allows you to:
- Block malicious software from running using customizable lockdown, safelisting, and denylisting policies
- Create dynamic policies by leveraging Trend Micro’s application categorization and reputation intelligence to reduce management overhead
- Correlate data from millions of application events to identify threats and maintain an up-to-date database of validated applications
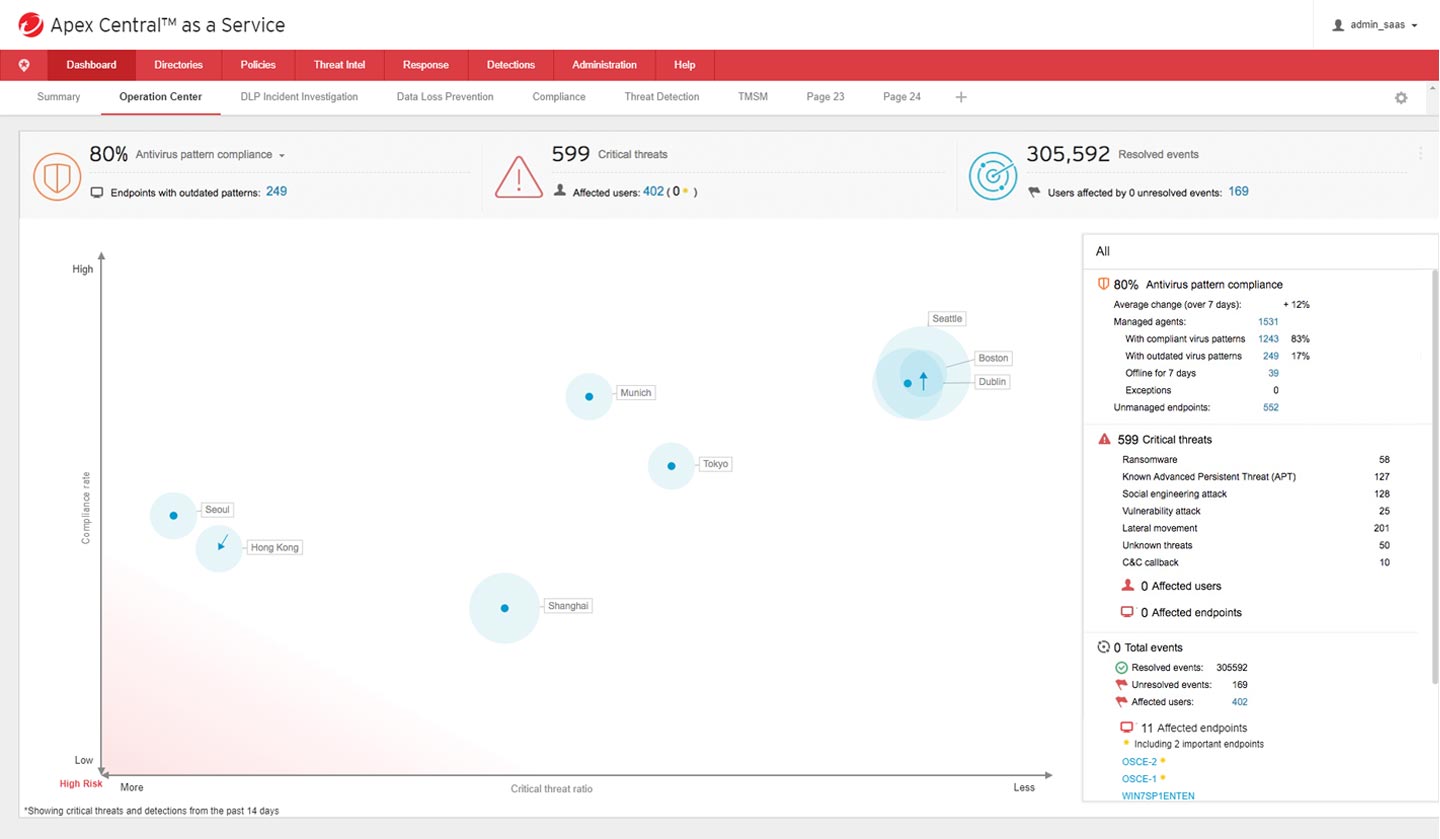
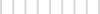
Centralized visibility and control
Enable consistent security management, visibility, and reporting across multiple layers of interconnected security through a centralized console.
Extend control and visibility across on-premises, cloud, and hybrid models
Improve protection, reduce complexity, and eliminate redundancy
Provide access to actionable threat intelligence from the Trend Micro™ Smart Protection Network™